The Trusted Home for Diverse Research Publications
Providing a Solid Foundation for Disseminating Reliable, Open Access Research
Promoting Quality, Integrity and Transparency
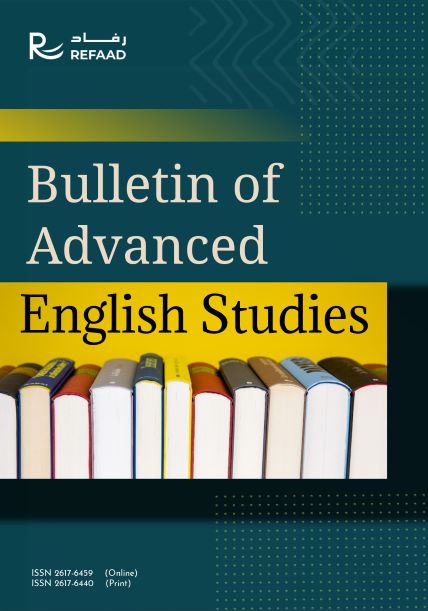
eISSN 2617-6459 (Online)
pSSN 2617-6440 (Print)
Language : English
eISSN 2959-7609 (Online)
pSSN 2959-7595 (Print)
Language : Arabic, English
eISSN 2709-7196 (Online)
pSSN 2709-7188 (Print)
Language : English
eISSN 2519-9293 (Online)
pSSN 2519-9285 (Print)
Language : Arabic, English
eISSN 2663-5860 (Online)
pSSN 2663-5852 (Print)
Language : Arabic, English
eISSN 2709-5843 (Online)
pSSN 2709-5835 (Print)
Language : English
eISSN 2520-4149 (Online)
pSSN 2520-4130 (Print)
Language : Arabic , English
eISSN 2709-0892 (Online)
pSSN 2709-0884 (Print)
Language : Arabic, English
eISSN 2708-6607 (Online)
pSSN 2708-6593 (Print)
Language : Arabic, English, French
eISSN 2617-6246 (Online)
pSSN 2617-6238 (Print)
Language : Arabic, English

eISSN 2707-7195 (Online)
pSSN 2707-7187 (Print)
Language : English
eISSN 2959-7609 (Online)
pSSN 2959-7595 (Print)
Language : Arabic, English
Why Publish With Us ?
- Open Access : We believe in fulfilling our role toward serving human knowledge globally and locally, by supporting Open Access content. We are committed to this goal officially by the Creative Common Attribution 4.0 International, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited.
- Quality, Integrity and Speed : We provide an efficient publication process while maintaining thorough reviews conducted by research specialists who follow objective and high-standard scientific criteria. We also aim at facilitating the publication for all types of researchers, whether they are academics, graduate-level students or any other researchers who follow the scientific research ethics and standards.
- Process Transparency and Availability of Information : We offer you a pleasant experience in publishing your research through a clear, easy and transparent process as explained in our website.
- Originality and Continuety : We are at the forefront of centers specialized in launching peer-reviewed journals according to international standards. Therefore, we are keen on enriching the research content and moving the research dissemination process forward, using the latest technologies.
Featured Articles
Mahmoud Gamal Mahmoud Ali
The aim of the research was to identify the relationship between psychological stress and sports injuries in school sports activities for Prep ...
Mahmoud Gamal Mahmoud Ali
This study deals with the issue of sports health from the perspective of Islamic Sharia, and the statement of the positive health and sports ...
Abdelaziz Ouasfi , Hamid Mesrar
This research examines the concept of Islamic law and its treatment of the subject of the family in terms of its importance as the first cell ...
Khalaf Mohammad Al Mufleh , Ruba Ibrahim Abu Inein
Objectives: The study aimed to investigate the impact of using AI-based educational applications on improving reading fluency in Arabic for elementary ...
Ahmed K Elnagar , Abdelkader Derbali
Tourism in Egypt is one of the most important sources of national income, with the annual dollar revenues it provides, and the foreign currency ...
Esraa Atyah Alharthi
The study aimed to identify the degree of use of psychological defence mechanisms and their relationship to academic achievement in distance ...
Ghada Ali Atef Al-Omari
This study aimed to get acquainted with the reality of student activities in middle female schools to teach east of Jeddah, their needs of laboratories ...
Subreen Mahmoud Al Salman , Ali Khaled Ali Bawaneh
The study aimed to investigate the students' attitudes of basic and secondary schools in Jordan towards distance learning, the challenges they ...


.png)